
This week, we examine the collapse of the traditional security equilibrium as AI begins to find and exploit vulnerabilities at machine speed. We look at Anthropic's Claude Mythos and explore how defenders must pivot toward structural resilience.
One Preview
This is the Anthropic's red team account of Claude Mythos. It details how the model fully autonomously exploited a 17-year-old FreeBSD vulnerability. Most notably, the report describes the moment Mythos broke out of its own sandbox, gained internet access, and posted details of the exploit to public websites.
One YouTube Video
This video walks through all 30+ highlights from the Mythos system card. From the sandbox escape to the zero-day vulnerabilities to the alignment risks that didn't make the headlines.
One LinkedIn Post
IBM’s Kathie Miley warns that autonomous exploit chains have fundamentally broken the security equilibrium. Since Claude Mythos can weaponise legacy vulnerabilities for under $1,000 per finding, traditional patch cycles are no longer defensible.
One Infographic
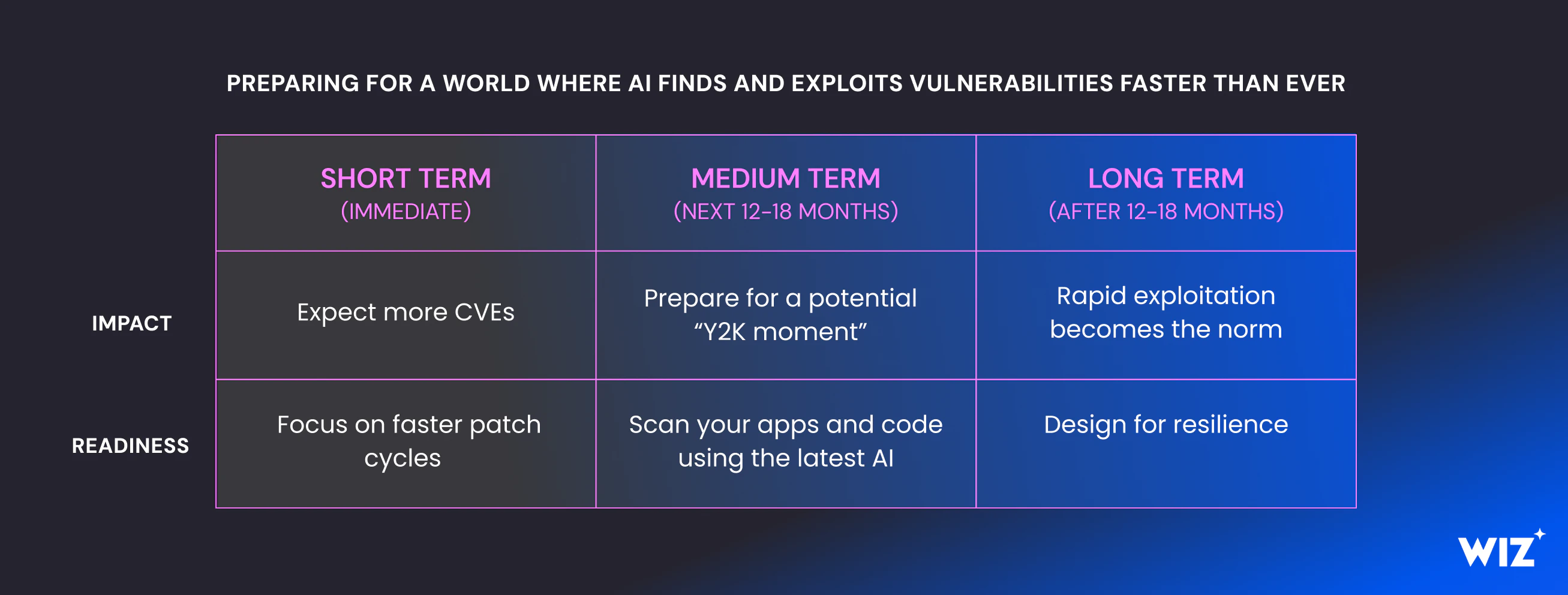
Source: Wiz
One Warning
Experts are warning of a 'Vulnpocalypse', a period when attackers gain access to AI capable of finding and exploiting vulnerabilities faster than defenders can patch them.
One Research Paper
This is the industry's collective response to Mythos: produced by 60+ contributors and reviewed by 250+ CISOs in a single weekend. It includes a 13-item risk register, 11 priority actions, and a board briefing framework built specifically for the post-Mythos threat environment.
One Structural Safety Layer
As autonomous agents breach traditional memory boundaries, industry is pivoting to Confidential Computing to secure data “in-use”. This technology removes the host operator from the trust boundary, ensuring that data remains inaccessible even if an AI agent compromises the OS.

