
This week, we explore why cloud migrations often introduce new security risks and how modern architectures can protect sensitive data without slowing adoption.
One Reminder
With International Data Privacy Day marked this week, this Forbes article makes the case that privacy has become a strategic business and leadership imperative. It examines how AI, connected systems, and emerging technologies are reshaping risk.
One YouTube Video
This AWS podcast explains why cloud migrations fail when security is bolted on, showing how poor asset visibility and technical debt create long-term risk. It explains why cloud-native guardrails and execution-time controls are essential to reduce exposure.
One Article
This article outlines the security and compliance risks of cloud migration. It shows how privacy-enhancing technologies help organisations migrate sensitive workloads to the cloud without expanding their attack surface.
One Whitepaper
This whitepaper provides a clear, policy-grounded overview of confidential computing and why protecting data during processingis becoming essential for cloud adoption.
One Infographic
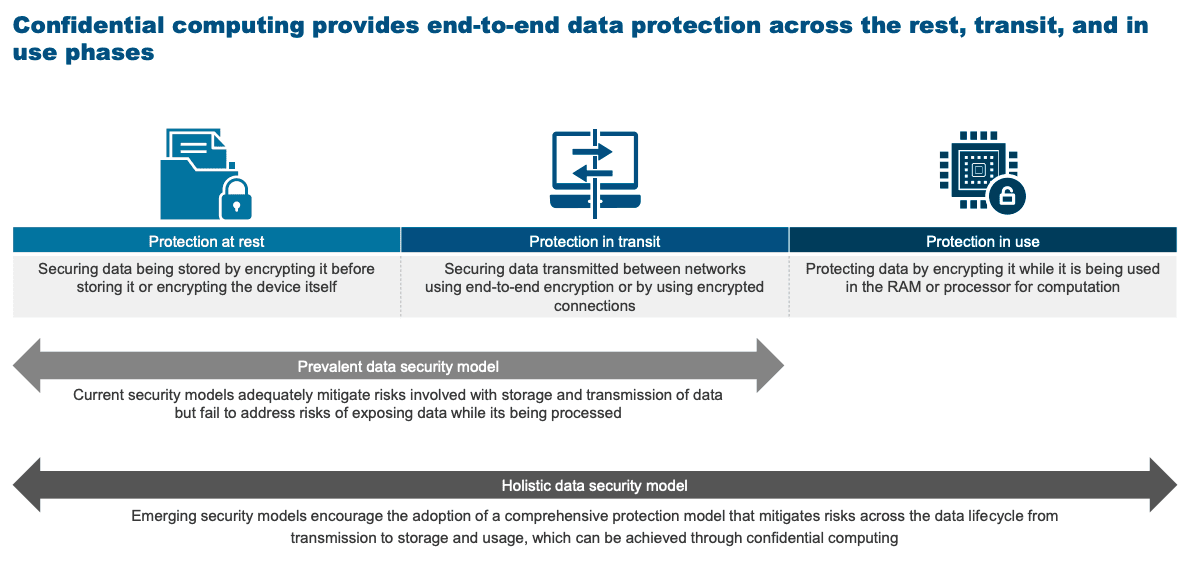
Source: Confidential Computing Consortium
One Explainer
This article shows how confidential computing supports decentralised data governance in multi-cloud environments, using TEEs and remote attestation to enforce security and compliance consistently across cloud providers.

